Berlin-based cybersecurity agency Cure53 discovered some safety flaws with Mozilla VPN apps throughout its newest safety audit.
After reviewing all of Mozilla’s purchasers, a complete of seven safety vulnerabilities have been found, two of which have been thought of important or excessive precedence. The VPN service now ensures that it has already addressed all of the potential dangers.
Unbiased audits have more and more grow to be a typical follow amongst VPN corporations that worth transparency and safety. That is the third time Mozilla has entrusted Cure53 with such a job, and it comes because the supplier launched new options, together with a brand new malware blocking system.
Mozilla’s blended outcomes
A workforce of 5 senior testers at Cure53 carried out a sequence of penetration assessments and software program inspections throughout Could 2023 for a complete interval of 21 working days. A white-box strategy was used to check the safety infrastructure and code sound of all Mozilla purposes, specifically MacOS, Linux, Home windows, iOS and Android VPN app.
Seven safety flaws, two excessive and 5 medium precedence, “contributed to the decidedly blended general impression obtained for the safety resilience of Mozilla VPN shopper purposes,” the report reads.
If the code construction was deemed “soundly composed” and freed from reminiscence corruption errors, specialists discovered a number of the VPN options to doubtlessly expose customers’ knowledge.
Essentially the most important vulnerability affected the Mozilla VPN iOS app. Checks confirmed that the WireGuard configuration saved within the iOS keychain was leaked to iCloud by way of gadget backups if customers didn’t explicitly select superior knowledge encryption. Mozilla claimed that Cure53 confirmed that this danger has been addressed by including an additional layer of encryption.
One other excessive precedence error was discovered on desktop as mozilla lowpnp the appliance didn’t sufficiently prohibit the calling software, doubtlessly permitting a malicious add-on to work together with the VPN and presumably even disable the VPN connection with out the person’s information. Once more, Mozilla assured to have addressed this danger as advisable by Cure53.
As talked about, Mozilla has reportedly patched all the opposite medium and low vulnerabilities as advisable by Cure53. Equally, the final safety audit reviewed in 2021 discovered main points in Mozilla VPN, all of which have been mounted in the course of the audit interval.
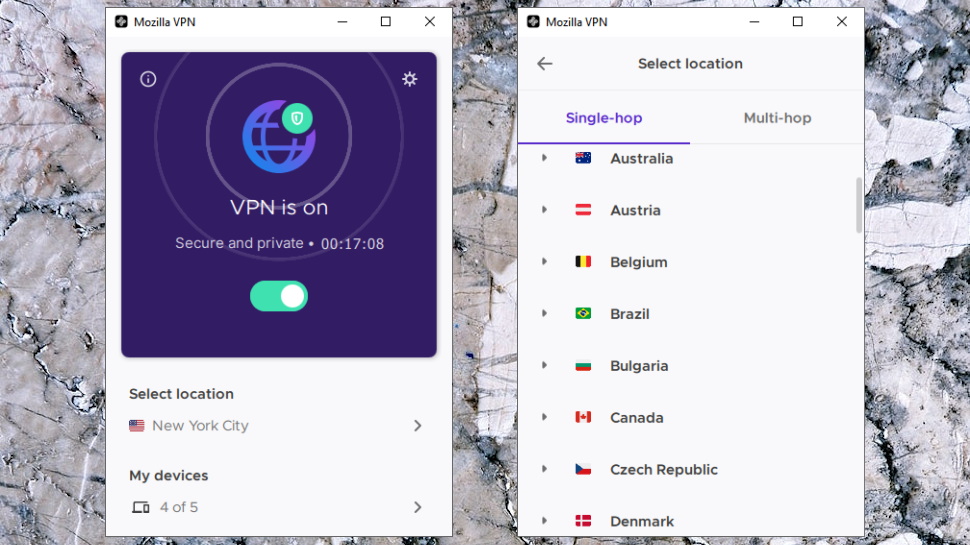
On a extra optimistic observe, Cure53 additionally praised a few of Mozilla’s options like split-tunneling and multi-hop connections, which relied on established know-how just like the Mullvad libraries and drivers. “The truth that these have been built-in from scratch minimizes the probability of rising weaknesses, with no important considerations to report beneath the assigned evaluation plan,” specialists wrote.
Mozilla is claimed to have determined to name within the third-party auditing agency once more earlier than the discharge of some new options. These embrace a malware-blocking software program launched in August, in addition to efficiency enhancements similar to server location suggestions, which have been built-in throughout its apps in June.
The supplier has additionally expanded its server community throughout 16 extra European nations, together with Denmark, Hungary, Portugal and extra.

